By Nate Nelson
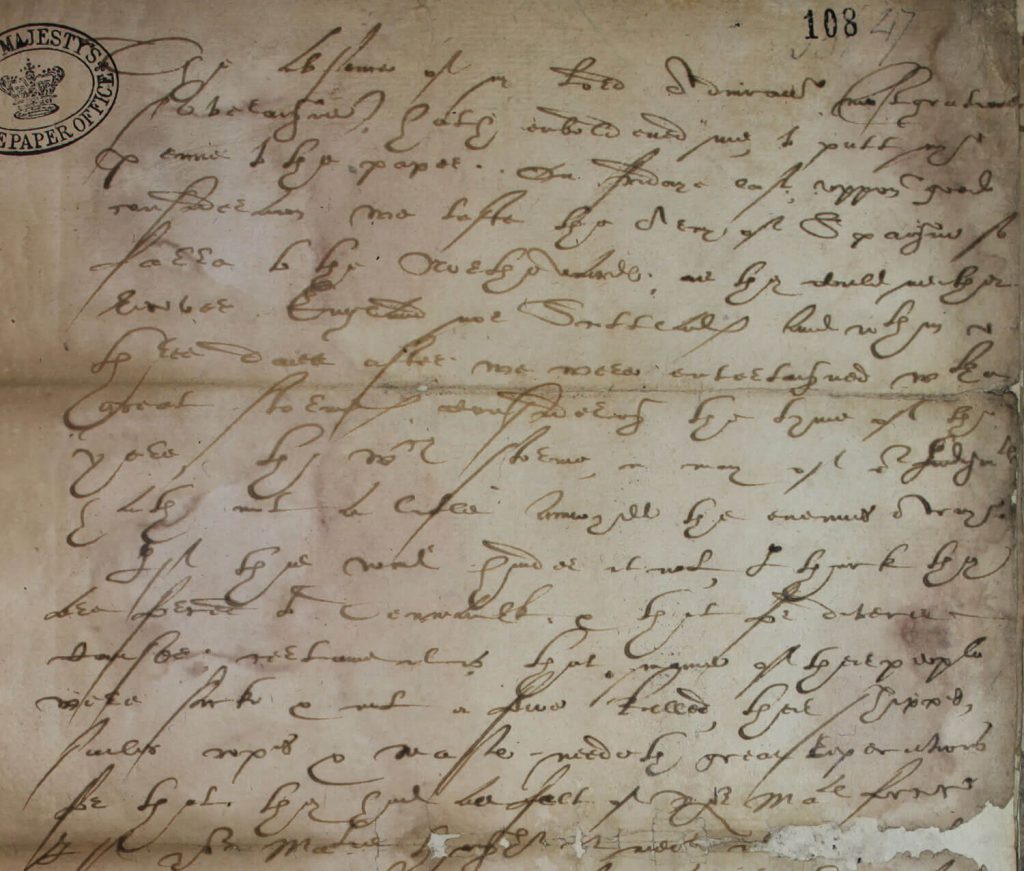
For 19 years Mary, Queen of Scots, had been under confinement by order of her cousin, Elizabeth I, Queen of England. Then, on July 14th of 1586, she got her ticket out–a letter from an ally:
“Myself with ten gentlemen and a hundred of our followers will undertake the delivery of your royal person from the hands of your enemies.”
The actual text would’ve looked something like this:
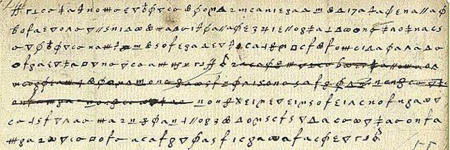
Gibberish, to the naked eye. A message, if you knew how to read it.
It turns out that spending two decades imprisoned is a pretty good way to learn about cryptography. Mary had furious thoughts and devious plots for her cousin and captor, but knew not to communicate in open letters, lest they be intercepted. So, just in case, she and her allies encoded messaging.
Specifically, they used a substitution cypher–a system wherein every letter, and some common words, were replaced by symbols. An ‘A’ might be replaced by a ‘/,’ a ‘B,’ ‘π.’ The Pope, ‘X,’ the King of Spain, ‘≠.’ Only an ally with the same set of rules knew how to convert between one and the other.
Except the system had one fatal flaw.
Secure Communication Today
In some ways, we today face the same challenges Mary did in 1586.
Individuals, enterprises and especially high-level government and military entities need to be able to communicate securely. But hackers on the internet are perfectly capable of intercepting messages sent between endpoints.
To ensure that doesn’t happen, one of two conditions must be met. Either:
- The line of communication must be 100% impossible to intercept, or
- The message itself must be 100% indecipherable
It’s very difficult to make the internet uninterceptable, so most protections focus on the latter condition. Like Mary of Scots, we use cryptographic mechanisms to encode messages traveling along wires, to prevent them from being readable should they be intercepted.
But like Mary, we’ve settled for imperfection. Algorithms can encode, but they can also decode. Encrypted messages can be reverse-engineered if they were encrypted poorly, or if the attacker has exceptional computing power at their disposal (say, hypothetically speaking, a futuristic quantum computer).
The Necessity of Secure Quantum Communication
The risks in traditional encryption have spurned a new approach: secure quantum communication through quantum key distribution (QKD).
QKD isn’t an upgrade over traditional cryptography, in the way modern algorithms are an upgrade of substitution cyphers. It is a different way of approaching the problem.
With QKD, information is transmitted in photons and encoded in quantum states. The details can get a bit complicated, but all you need to know is this:
By the laws of quantum physics, an attacker simply cannot read any of the quantum-encrypted data they intercept. Like a letter that disappears if it’s opened by the wrong person.
But QKD has significant weaknesses. Although provably secure, QKD is incompatible with the Internet’s existing infrastructure, requiring cost-prohibitive investments in new hardware for a real-world implementation. And information cannot be transferred fast enough to provide adequate service levels.
This is why companies like Quantropi are investing in quantum-grade cybersecurity to address today and tomorrow’s threats to data security.
The Consequences of Insecure Communication
Mary, Queen of Scots could’ve used some of that.
The fatal flaw in her system was simple: in order to coordinate secret codes with allies, she needed to send them the answer book. Like an insecure key sent over the internet, any enemy positioned in between transmitter and receiver would receive all the information necessary to decode her cipher.
And, little did Mary know, her courier was a double agent. She sent a codebook to the French ambassador to England and, unlike secure quantum communication, it didn’t self-destruct when the courier opened it mid-transit. The rest is history.
Learn more about Quantropi’s TrUE Quantum Secure Solutions here.
Feature image source: National Archives UK.